Private Pain Tracker: Secure Symptom Logging Without Surveillance
What makes a pain tracker truly private
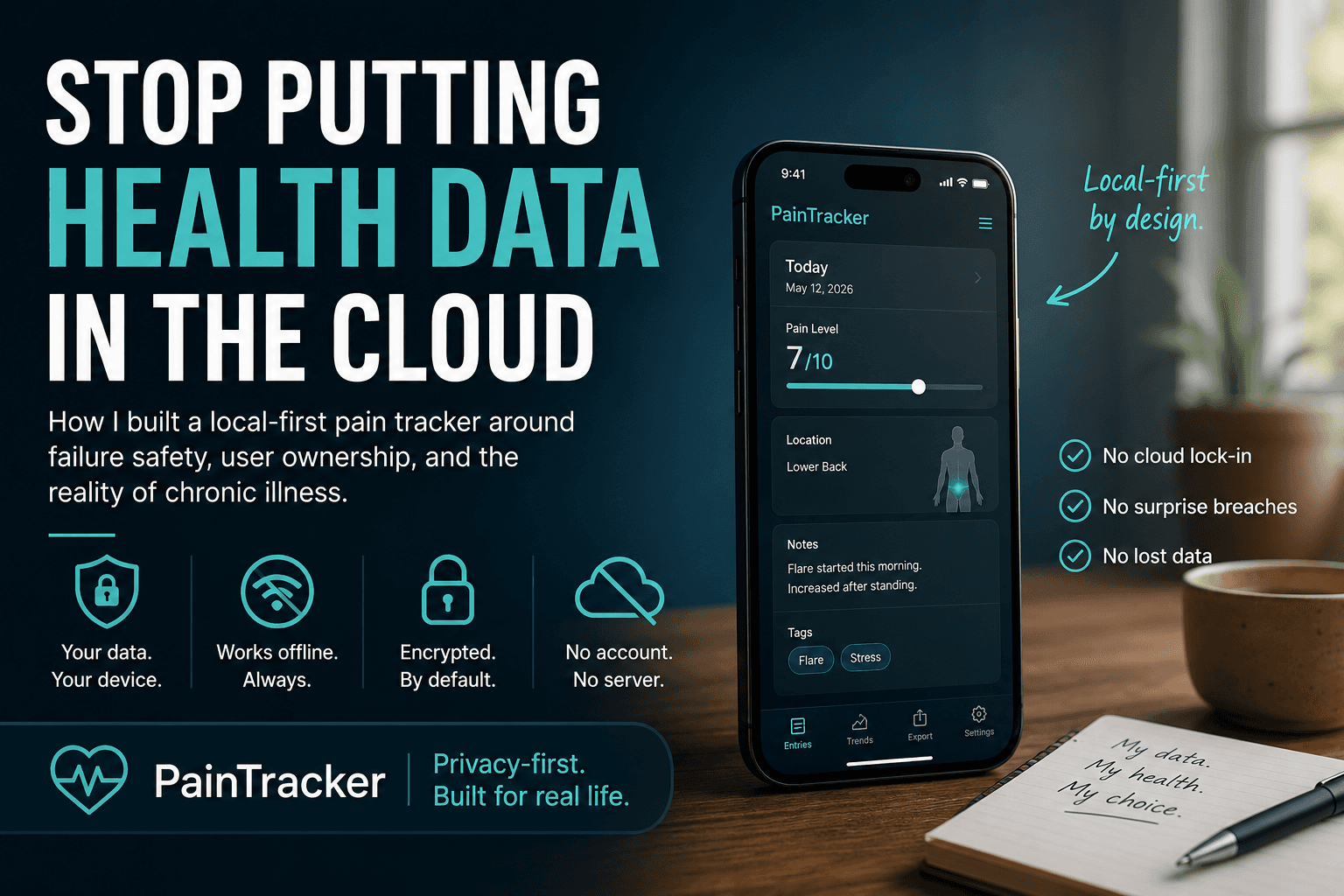
Privacy in health apps is not a feature toggle—it is an architectural decision that shapes every layer of the application. A truly private pain tracker stores no data on external servers, requires no account creation, and cannot be subpoenaed because there is nothing to subpoena. The data lives on your device, encrypted with your passphrase, and leaves only when you explicitly export it.
Many apps claim privacy while collecting analytics, usage metrics, or crash reports that contain identifiable health information. A private tracker must go further: no telemetry by default, no third-party SDKs that phone home, and no advertising identifiers. PainTracker achieves this through a zero-knowledge architecture where the server serves static files and has no database, no user accounts, and no API endpoints that receive health data.
The distinction matters because health data privacy is not abstract. Your pain diary may contain information about medication use, mental health, functional limitations, or workplace injuries—all of which can affect employment, insurance, custody, and legal proceedings if exposed.
Encryption that protects your entries
PainTracker encrypts all health data at rest using a key derived from your passphrase through a standard key derivation function. The encryption happens entirely in your browser before data is written to IndexedDB. No plaintext health data is ever stored persistently.
This means that even if someone gains physical access to your device, your pain entries are protected by your passphrase. The encryption key is never stored—it is re-derived each time you unlock the app. There is no "forgot password" option because there is no server that holds a copy of your key. This is a trade-off: you must remember your passphrase, but in exchange, no one else can ever access your data without it.
The encryption implementation is open source, auditable, and uses standard Web Crypto APIs rather than custom cryptographic code. Security through obscurity has no place in health data protection—PainTracker relies on proven algorithms and transparent implementation.
Why cloud-based trackers compromise privacy
Cloud-based pain trackers create a persistent copy of your health data on someone else's infrastructure. Even with encryption in transit, the data typically exists in plaintext on the server side—accessible to employees, subject to law enforcement requests, and vulnerable to breaches. Many health apps have been found sharing data with advertisers, analytics companies, or data brokers despite privacy policies that suggest otherwise.
The fundamental problem is incentive alignment. Companies that operate cloud infrastructure need revenue to pay for servers, and health data is extraordinarily valuable to advertisers, insurers, and employers. Even well-intentioned companies face pressure to monetise data or may be acquired by entities with different privacy commitments.
A local-only tracker eliminates this entire category of risk. There is no server to breach, no employee who can peek at records, and no business model that depends on data access. The incentive alignment is clean: the app exists to serve you, not to extract value from your health information.
Privacy features patients actually need
Beyond encryption, practical privacy requires features that address real-world threats. PainTracker includes a panic mode that quickly hides the application—useful in situations of domestic coercion or workplace surveillance. The app can be dismissed without leaving visible traces of pain tracking on screen.
Selective export controls let you share specific date ranges and data fields without exposing your entire history. This is essential for medical appointments where you need to share relevant data with one provider without giving them access to everything you have ever recorded. You control the granularity: share a week, a month, or a specific set of entries.
The application also avoids creating unnecessary digital artifacts. There are no push notifications that could reveal pain tracking to someone glancing at your phone, no email receipts, and no calendar integrations that leak health information into shared accounts.
Accessibility and private tracking
Privacy and accessibility are not competing concerns—they reinforce each other. People with disabilities are disproportionately affected by health data exposure, facing discrimination in employment, housing, and insurance. A private pain tracker that is also accessible ensures that the people most in need of privacy are not locked out by poor design.
PainTracker targets WCAG 2.2 AA compliance with keyboard-navigable interfaces, screen-reader support, sufficient colour contrast, and touch targets sized for users with motor impairments. The trauma-informed design philosophy means the app avoids blame language, reduces cognitive load, and offers user control over the tracking experience.
Open source as a privacy guarantee
Privacy claims are only as trustworthy as their verifiability. PainTracker is fully open source, meaning anyone can inspect the code, verify that no data is sent to external servers, and confirm that the encryption implementation is sound. This transparency is not a marketing gesture—it is a structural commitment to accountability.
Open source also means the community can identify and report vulnerabilities, suggest improvements, and fork the project if the original maintainers ever compromise on privacy. Your trust is not placed in a company's promises but in code that anyone can read.
Building a private health record over time
A private pain tracker becomes more valuable the longer you use it. Months or years of consistent entries reveal patterns that no single appointment can capture—seasonal variations, medication effectiveness trends, activity-pain correlations, and recovery trajectories. This longitudinal data is clinically powerful and deeply personal.
Because PainTracker stores data locally and exports in standard formats, your long-term records are not locked into a proprietary ecosystem. You can export your entire history at any time, maintain backups on your own terms, and share data with new providers as your care team evolves. Privacy and portability are both served by the same local-first architecture.
Frequently Asked Questions
Does PainTracker collect any personal data?
No. PainTracker has no server-side database, no user accounts, and no analytics that collect personal information. All health data stays on your device.
Can my employer access my pain tracking data?
No. Your data is encrypted on your device and never transmitted to any server. There is no database for anyone to request access to, including employers and insurers.
What happens if PainTracker shuts down?
Your data remains on your device. PainTracker is also open source, so the code remains available for anyone to run independently. Export your data regularly as an additional safeguard.
Is PainTracker HIPAA compliant?
PainTracker implements HIPAA-aligned controls including encryption at rest and access controls. However, as a local-only tool with no server-side data processing, traditional HIPAA compliance frameworks do not directly apply.
Try PainTracker free — offline, encrypted, clinician-ready pain tracking.